
When you hear references to Watson, does your mind think of Sherlock and Dr. Watson? In the case of IBM Watson, the assistant is more like Sherlock than Dr. Watson in practice. IBM Watson learns about customers and consumers in the same way that humans learn. Watson studies and visits with people, asking questions and building knowledge from the answers. The knowledge base from the interactions that span over many consumers with a myriad of tastes, personalities and intelligence is extremely diverse and powerful for businesses. Let's look at the challenges, solutions and outcomes from using the power of Watson across different businesses.
As retail customers expect mobile shopping applications, Macy's customers expect a mobile application different from the average mobile shopping application. The American retail giant has unique stores and wanted a mobile app that reflected and addressed the unique nature of Macy's stores.
Watson provided the right answer for a unique mobile shopping experience. Macy's On Call service based on Watson offers the mobile shopping application that Macy's customers expect.
Macy's built and deployed On Call across 10 cities. As Watson learns the habits and preferences of customers, On Call will provide the foundation for greater usage related to products, services and navigating customers through different store layouts.
Although the number of tax refunds was higher for H&R Block customers, H&R Block wanted to raise the number.
In order for H&R Block to increase the number of customers receiving more tax refunds, H&R Block needed to put the power of thousands of tax professionals against the extremely complicated tax code spread over thousands of pages, with thousands of equally complicated changes made regularly, into the hands of clients who wanted the best tax refunds from their tax returns.
Watson provides the answers to thousands of questions and covers thousands of topics from the intelligence and expertise of literally thousands of tax professionals. Watson provides the complexity necessary to combine all the knowledge into a workable platform that ensures clients will have enormous resources to address all the areas of tax preparation.
Customers gain the benefits of all the expertise and intelligence funneled into a massive chart created from the customer interview with a tax professional. The tax professional benefits from the same enormous chart of options designed for the customer.
When faced with the enormous number of products available from Staples to address the needs of customers, the office supplies giant needed an easy way for customers to navigate the products and services available. Staples needed more: The company needed to set itself apart in the highly competitive online products business.
The Staples "Easy Button" provides simple avenues to reach the products and services that meet customer needs. With IBM Watson, Watson can learn the needs of the customers by watching their buying habits and then making recommendations to improve the customer experience
As Watson continues to learn more and more about the customer, it makes recommendations to fill the customer needs, rather than the customer hunting for solutions alone. Watson has the updated knowledge of new products and customer needs that ensure consumers will have the latest suggestions tailored to their needs. IBM wanted more than just artificial intelligence, but actually augmented, to include human interaction as well. The combination of virtual and human interaction is a powerful tool for businesses deploying Watson.
Autodesk wanted to build face-to-face interaction with customers online. The company wanted the same success that builds customer loyalty from face-to-face interactions. Such interactions provide nonverbal reactions that virtually empathize with customers.
The 3D design software company created the Autodesk Virtual Assistant (AVA), powered by Watson to provide the face-to-face interaction virtually as well as intuitive chatbot responses. IBM Watson Conversation API supports AVA in handling hundreds of types of requests by learning customer needs from live help calls. The IBM Watson tone analyzer is a necessary part of the system to sense the customer emotions for AVA.
AVA can utilize customer emotions, a knowledge base developed from actual help desk recording, to handle over 40,000 customer help requests. AVA demonstrates performance virtually that would require costprohibitive physical agents.
When customers wanted to find that perfect jacket, customers were met with a huge selection of jackets to sift through until the perfect jacket is found. North Face wanted to simplify that process and get the customer the right jacket that fit the individual.
North Face decided virtual assistance would steer the customer to the right product. Watson listens and asks the right questions to help determine what jacket fit the customer the best.
North Face had sales conversions at an impressive 75% for over 50,000 users covering two months. The outcome of the testing led to a full mobile app.
The challenge for many businesses, especially in the online environment, is making a personal connection. Companies need to connect with the customer virtually as they would face-to-face. Businesses need customer service that builds from visiting with the customer about their needs and wants in products. Advertising requires that same personal connection for reaching the potential customer.
Watson Ads provide the connection through learning customer needs by asking questions and listening to the responses. Watson advertising allows two-way conversations that mine the data from a customer that teaches Watson about their needs, then tailoring the advertising to those needs.
With Watson Ads, businesses and marketing can achieve the personal connection with consumers. Anyone that has attended web seminars or online training understand the difficulty in making that vital connection. Watson fills that void in making the connection between customer and advertising by drawing the potential customer into the conversation.
In May 2017, over a million Gmail users were hit by a phishing scam - a scam that appeared to originate from Google itself.
Although the attack appeared to be sophisticated (due to its ingenuity and apparent authenticity), it was actually simple.
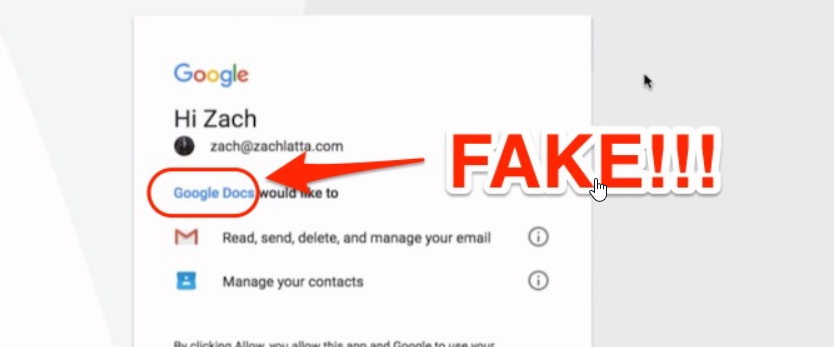
The hacker built an app, named it "Google Docs" and registered it with Google. The app sent Gmail users an email purporting to be a Google Docs invitation - complete with the language, design and "Open Docs" button on the real Google Docs app. Once the user clicked this button, it took them through a series of actual Google sign-in pages (Google allowed the hacker to leverage its OAuth process within the app) where it requests for privileges to access passwords, emails, contacts and other Google account information.
Aside from compromising account data, the phishing scam also used victims' Gmail accounts to send emails to their contacts, further spreading the worm. Initial analysis of the source code shows that the worm may have been designed only with propagation in mind, though the hacker may have had more malicious intentions in mind.
Since the tech giant shut down the fake Google Docs app in record time (within 30 minutes), the hacker(s) only had a few minutes to access the data on victims' accounts. But a few minutes is more than enough time to steal a staggering amount of information, especially since over a million Gmail users were exposed to the scam.
Though it's unclear how the hacker managed to insinuate a fake Google Docs app into the OAuth ecosystem, Google has since taken steps to prevent such from ever happening again.
Google leveraged machine learning-based detection, removed all the fake pages, pushed updates through safe browsing, implemented email attachment scanning and other security measures to prevent the creation and spread of similar phishing scams
The tech giant regularly takes down applications that violate its User Data Policy and periodically reviews potential OAuth abuse. It also warns users to directly install its apps from the Apple App or Google Play stores or access them from within the Google site.
Victims of the scam should change their passwords and check third-party apps that may have been granted access to their Google account. They should also confirm if there was sensitive data in their inbox at the time of the attack since the information may eventually turn up for sale on the dark web
The Google Docs phishing scam shows that no company, application, service or IT infrastructure is immune to phishing attacks. Even more worrisome is the fact that the scam didn't use fake websites or malware to trick users into giving up their passwords.
Users fell for the scam because it originated from a trusted website and as such, they were tricked into granting permissions and privileges to an innocuous-looking third-party app.
Phishers can leverage real accounts to develop third-party plugins that interact with users and lure victims into giving up their information through genuine web pages. This is the future of phishing and security technology vendors are ill-equipped to deal with it